Lesson 34: DevSecOps - Shifting Security Left in Kubernetes
What We’re Building Today
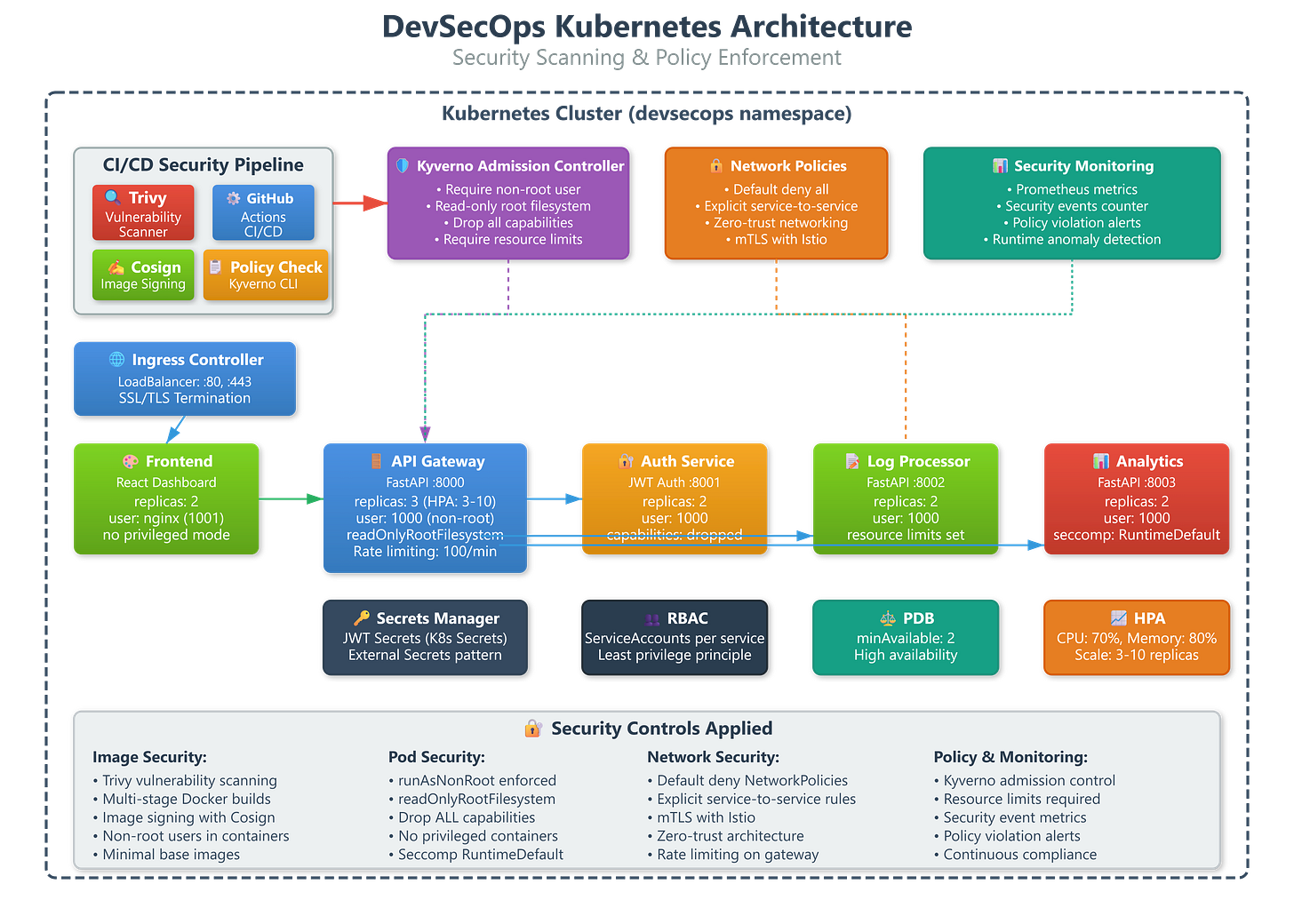
A production-grade DevSecOps pipeline implementing:
Automated vulnerability scanning with Trivy integrated into CI/CD (blocks deployments with critical CVEs)
Runtime policy enforcement using Kyverno for pod security standards and image validation
Zero-trust networking with Calico network policies and mTLS service mesh
Secrets management with HashiCorp Vault integration and encryption at rest
Complete audit logging of security events and policy violations across the cluster
Why This Matters: The $4.2M Misconfiguration
In 2023, a major fintech company deployed a microservice with a known Log4Shell vulnerability (CVE-2021-44228) that passed CI/CD because security scanning happened after deployment. The breach cost $4.2M in incident response and regulatory penalties. Meanwhile, Capital One’s 2019 breach stemmed from excessive IAM permissions - a policy that should have been caught by automated enforcement.
The shift-left security movement emerged because manual security reviews don’t scale to 50+ deployments per day. Netflix deploys 4,000 times daily across 100,000+ containers - every deployment must pass automated security gates or the pipeline fails. At that velocity, security can’t be a separate phase; it must be embedded in every build, every deployment, every runtime decision.
Traditional security approaches create a fundamental conflict: developers want velocity, security teams want assurance. DevSecOps resolves this by making security automated, fast, and transparent. When Shopify integrated Trivy scanning, they caught 847 critical vulnerabilities in existing images within the first week - vulnerabilities that had been running in production for months.